Editor's Note: First published way back in 2017, this article is still an excellent source of advice on protecting IP during times of change.
When it comes to departures or transactions, employment agreements and data security can only get you so far without a proactive plan.
Major corporate transitions are never easy. Whether it's an employee departure (key executive, large workforce reduction, or others) or a corporate transaction (merger, acquisition, divesture), there are lots of risk factors to a company every time a major transition takes place.
During such transitions, one such risk factor that oftentimes goes undetected is the vulnerability of your organization's valuable IP. Employment agreements and data security can only get you so far without a comprehensive proactive plan. In fact, according to a survey by The Ponemon Institute and Symantec, nearly 60 percent of people who had recently left or lost their jobs admitted to taking confidential company information on their way out the door.
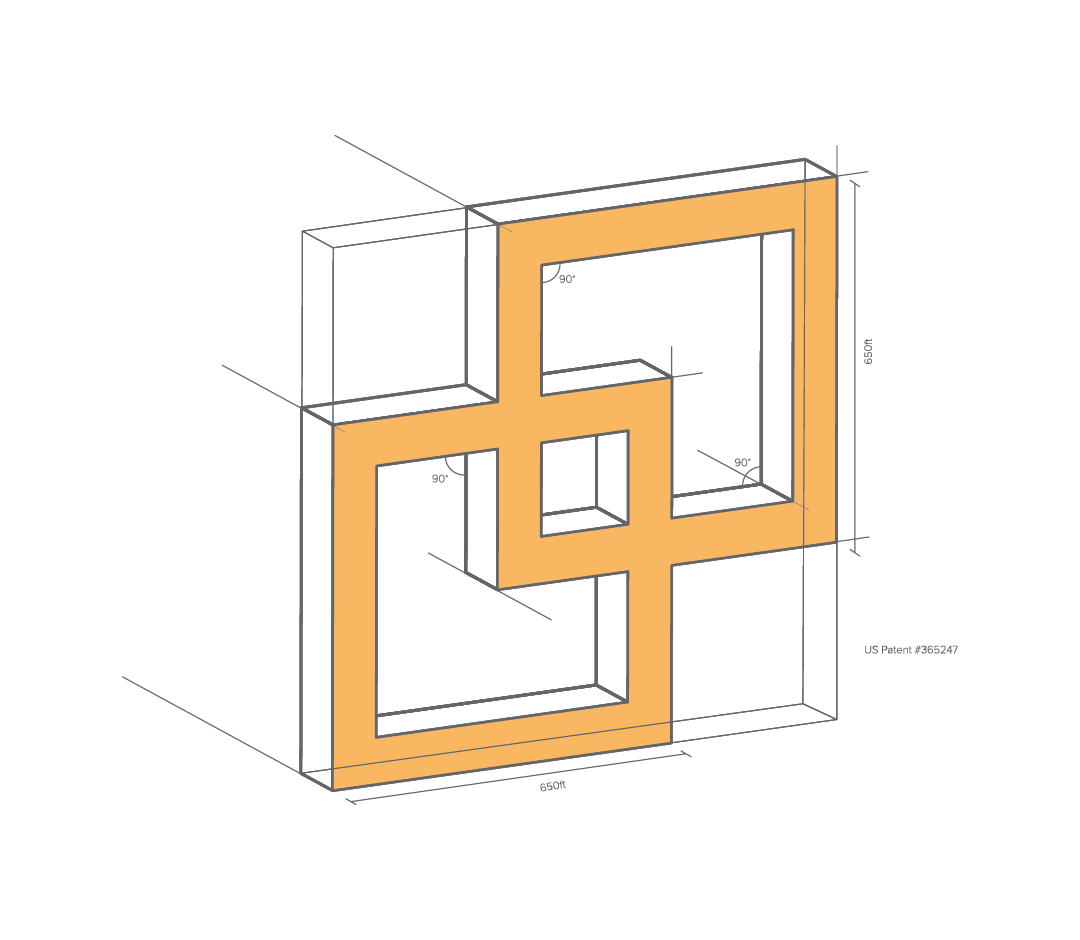
The most common example of this information vulnerability is the theft of trade secrets—such as personal contact information, customer lists, pricing information, and business procedures—but in the case of these corporate transitions, it could also include other types of intellectual property, such as the misappropriation of copyrights, trademarks, and patents. The loss of sales, the expense of legal fees, and the time of tracking down and recovering stolen IP are only some of the examples this loss of IP can harm a company.
Here are five ways to secure and protect your company's IP during a corporate transition.
1. Know your data.
Start by having a data map in place, as well as a clear data preservation plan. This will allow you to have an overall understanding of the different types of data your team members utilize and where that data resides. With this picture in front of you, identify key risk points. These could be data that is readily accessible and the data most meaningful to you as a company.
Another key need is to know how your employees use their data. For example, do your employees use personal email for work (even if you tell them not to) or do they utilize text messages for work purposes?
2. Centralize and audit data collected for litigation or investigation purposes.
Understandably, there is significant concern among corporate executives over the practice of sending data to a variety of locations in the middle of a litigation dispute. It's best to limit these data stores and to make sure they are vetted for security purposes. The same vetting used for other IT related initiatives and vendors should be used for these third-party resources. You do not want a situation where you send the very data you are trying to protect only to have it breached at one of these vendors.
Also, make sure that the appropriate team gets regular reporting on where the data is stored, how it is stored, if it really needs to be there, and specifically how the data will be removed once it's off legal hold. At the conclusion of the transitional event, be ready to verify that the data has been removed in a manner consistent with the corporate retention policies.
3. Identify key IP in transactions.
Corporate transactions are often exciting events that can reshape a company's future; however, given the fast pace and often large number of employees and amount of data at issue, it can be difficult to manage appropriately and efficiently. For example, companies can search through large sets of data to identify particularly key documents that could prove devastating to your company down the road.
If your organization doesn't have adequate internal data security capabilities, reach out to an outside service provider that can go behind the network, identify your valuable IP and make sure it is not lost during a divestiture or M&A activity. In fact, it's particularly crucial in divestitures to make sure IP unrelated to the divestiture is not accidentally transferred to the new entity.
4. Know your roles and responsibilities.
It's important to have clarity about the people within your organization who are best qualified to manage key aspects of data security during these transitions. For example, who in your IT or legal department will handle coordination of any data production requests during a transition event? Who on your IT or legal team, or from an outside service provider, will handle the collection of any high-value data? For example, if your organization is a Silicon Valley company that doesn't want to stifle innovation by limiting access to certain tools, then line up a consistent outside resource that has familiarity with similar companies. Finally, assign an individual who will be responsible for managing any necessary "holds" and establish a protocol for tracking all holds.
5. Protect against data loss in employee transition.
The first job of the individual/team tasked with being in charge of protecting data loss is to identify key employees who have access to sensitive company data and/or potentially relevant data. For the specific event of an employee transition into a new position or departure to a different company, preserve copies of your employees' machines.
Also, identify any proactive measures you want to take during departures and transitions so that sensitive company data—including any data that may be relevant to a hold—is not deleted or transferred. There are also tools available in the market place that allow for the monitoring of activities for high risk individuals or data sets.
Conclusion
Corporations are sometimes unprepared for the danger that a major corporate transition can pose to your intellectual property. Employee departures, workforce reductions and corporate transactions are common examples of events that can make for a perfect storm of IP security threats. It's important to be proactive in implementing some best practices in order to protect your IP before it walks out the door.
The opinions expressed in this article do not necessarily reflect the views of O'Melveny or its clients, and should not be relied upon as legal advice.
John Del Piero is vice president of global e-discovery solutions for Lighthouse. John focuses on developing integrated partnerships with law firms and corporations to manage fast-moving, complex litigation and investigations with varying privacy and regulatory restrictions.
Anthony Cardine directs O’Melveny & Myers practice support department. The group consults with the firm’s legal teams and clients globally on the strategic application of technology to legal challenges. Anthony provides consultative services to clients in the areas of litigation readiness, electronic discovery and legal technology solutions.