RelativityOne

One powerful platform, endless possibilities
Empowering you to get the most out of your data
A versatile platform for any data challenge
RelativityOne seamlessly scales to meet projects of any type and any size, empowering you to tackle legal data challenges far beyond litigation.
Transparent and ethical AI
We understand AI brings both opportunities and challenges. That’s why we’ve thoughtfully designed our solutions to transform your work while keeping you in complete control.
A solution, and team, that has your back
Trusted by law firms, corporations, and legal service providers worldwide, RelativityOne helps you stay ahead with unparalleled security, performance, and support.
Tackle any legal data challenge in a single solution
No matter what data challenge comes your way, you can leverage the power of RelativityOne to get the insights you need across a wide variety of diverse legal, investigative, and compliance challenges.
RelativityOne for Litigation
Privilege Review
Reduce disclosure risks with AI-powered privilege decisions and log support.
RelativityOne for Investigations
Empower your in-house team to find the most crucial data sooner.
- Work across departments effortlessly with RelativityOne, making collaboration simple and effective.
-
Collect necessary data directly from the top cloud platforms.
- Automatically reduce duplicate and irrelevant documents, view data in native chat applications, and detect behaviors of interest.

RelativityOne for Regulatory Requests
Navigate high-stakes projects and meet critical deadlines with confidence.
- Swiftly find and produce all relevant material for complex projects such as second requests and antitrust investigations.
-
Ensure compliance and protect sensitive data.
RelativityOne for Data Breach Response
Respond to breaches quickly and accurately, leveraging AI to save time when it matters most.
- Quickly find documents containing personal information and provide an initial assessment of the impacted PI and entities.
-
Create recommended notification lists to act fast, avoid fines, and maintain trust by sending out timely notifications.

Work faster and smarter, every step of the way

Efficiently review documents of any type, on any scale
Whether you’re looking through emails, spreadsheets, chats, prompt-and-response conversations, or PDFs – we make it easy to get to the insights that matter most.

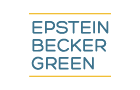
Transform your project with AI
Rely on advanced AI capabilities to meet aggressive deadlines, get better insights faster, protect privileged material, build your case story, and more.
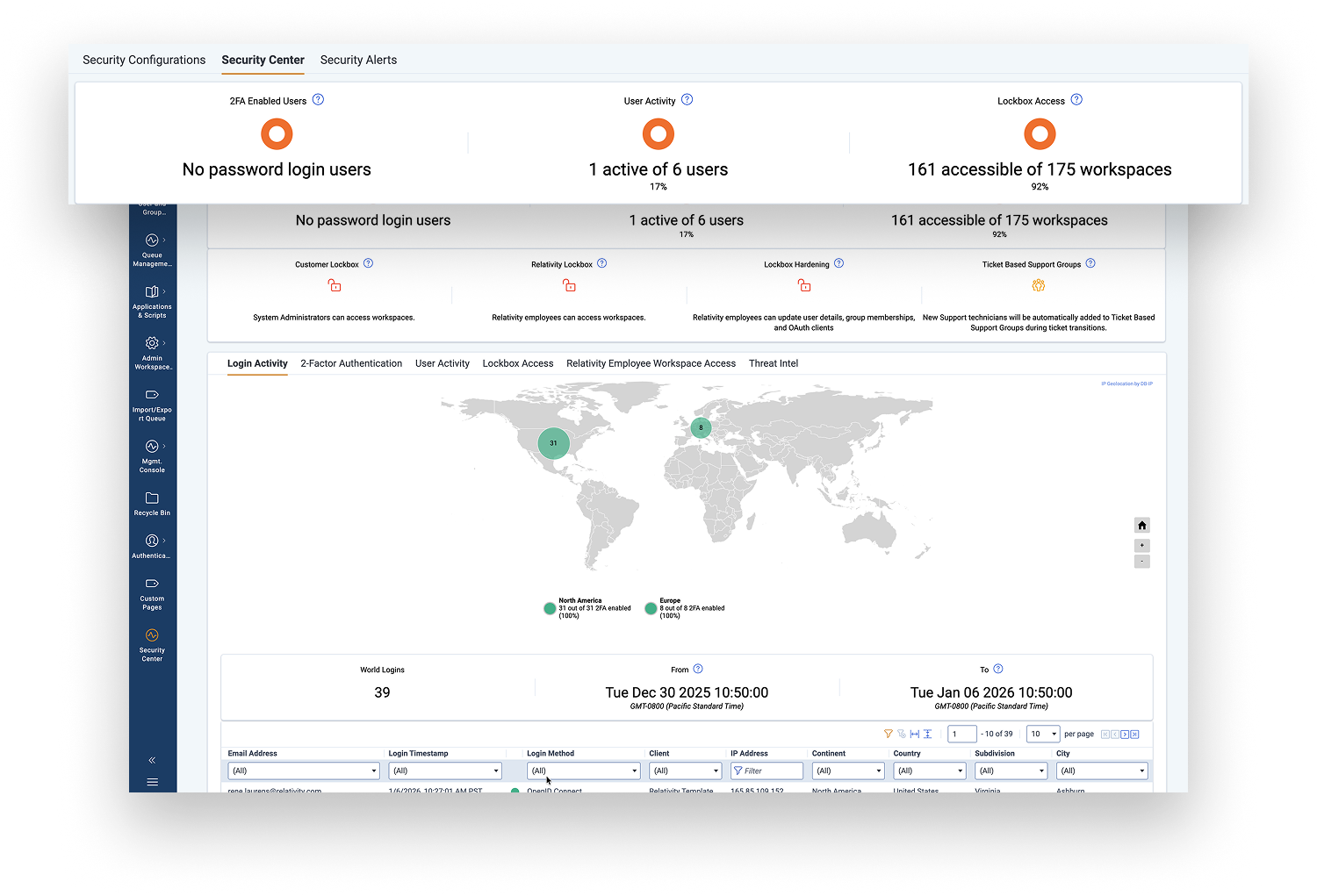
Keeping your most sensitive data protected
We build security into every step of our product development lifecycle and give you the insights and tools you need to stay secure.
Expand your business and collaborate on a global scale
RelativityOne is available in 17 countries, including some of the most privacy-forward, and supported by substantial investment in SaaS-based infrastructure. Choose where you want your data to live, enjoy one unified version of the software, and enable seamless collaboration around the world.
See what RelativityOne can do for you.
We’ve enhanced the experience in the platform and beyond. Benefit from 24/7/365 human support, faster implementation, and flexible pricing tailored to your needs.
Looking for more about RelativityOne?
Relativity named as a Leader in End-to-End eDiscovery
The most recent IDC MarketScape report evaluated e-discovery vendors worldwide and positioned Relativity as a Leader in the space.
Learn More